The author discovered a critical vulnerability at Samco Securities that exposed sensitive KYC documents for approximately 900,000 customers due to an insecure URL pattern. Despite reporting the issue in August 2024, the company largely ignored the researcher and only secured the data 64 days later following an escalation to CERT-In. This 64 day delay is exceptionally poor and stands way beyond the reasonable disclosure time typically followed in the cybersecurity industry. Samco ultimately declined to provide any formal acknowledgment for the report, even though the exposure included highly sensitive files like Aadhaar cards and bank statements.
In August 2024, I came across a tweet discussing how many exposed databases are openly indexed on Google and can be found using simple search techniques, often referred to as "dorking." Out of curiosity, I decided to explore these methods to understand the extent of such vulnerabilities.
Using the query filetype:pdf "aadhar", I discovered a publicly accessible PDF belonging to a customer of Samco, a stock broking company. The document contained both an Aadhaar card and a PAN card. Upon closer inspection, I noticed that the URL for the PDF ended with a 7-digit number. Modifying this number slightly revealed additional customer documents.
Further investigation showed that many sensitive files were accessible, including:
- Aadhaar and PAN cards
- Salary slips and bank statements
- Income Tax Returns (ITRs), passbooks, and blank cheques
To get a sense of how bad this was, I developed a Python script to test a range of these 7-digit numbers. The script revealed that approximately 10% of the tested URLs led to valid documents. With 9 million possible 7-digit combinations, this suggested that around 900,000 customer records could be publicly accessible. I manually verified approximately 2,500 records to confirm this 10% success rate before I forced myself to stop and start writing an incident report.
Initial Report to Samco
On August 18th, 2024, I reported the vulnerability to Samco via email. The email outlined the nature of the issue, the types of data exposed, and the potential scale of the breach. I requested an acknowledgment of receipt within 36 hours and provided details on how to contact me securely for further technical information.
Date: Sun, 18 Aug 2024
From: returntoshiganshina <returntoshiganshina@protonmail.com>
To: compliance@samco.in, escalations@samco.in
Subject: [15] URGENT: Critical Customer Data Exposure Discovered
Dear Samco Management,
I am writing to report a critical security vulnerability I have discovered on your website that exposes sensitive customer information.
Details of the vulnerability:
1. Nature of the issue:
Your website is exposing confidential customer data publicly.
2. Types of data exposed:
This includes, but is not limited to, Aadhar cards, PAN cards, bank statements, salary statements, signatures, phone numbers, and addresses.
3. Method of discovery:
The data, presumably used for KYC and signing up, is stored as PDFs online, but is not password protected and appears to be indexed by search engines. After discovering one exposed record, I noticed a pattern in the URL structure that made other records accessible.
4. Scope of the issue:
Based on the URL structure and initial findings, I have estimated that potentially tens of thousands at the least or realistically, 9 lakh customer records are exposed.
The seriousness of this vulnerability cannot be overstated. The severity of this issue cannot be overstated. It poses a significant risk to your customers' privacy and financial security, as well as to your company's reputation.
Please note that due to the severity of this vulnerability, if I do not receive a satisfactory response within 72 hours, I may be obligated to report this issue to CERT-In to ensure appropriate action is taken to protect customer data.
I request that you:
1. Acknowledge receipt of this email within 36 hours.
2. Provide me with information about your bug reporting or responsible disclosure process.
3. Take immediate action to secure the exposed data and fix the vulnerability.
I am willing to provide more detailed technical information to your security team through a secure channel of your choosing. I want to assure you that none of this data or information has been shared with any third party, downloaded, or stored and am prepared to cooperate fully with your security team to help address this vulnerability promptly and securely.
I respectfully request a secure email channel to contact the appropriate team regarding this matter.
I look forward to your prompt response and action on this critical issue.
Sincerely,
A concerned Cybersecurity Enthusiast.Samco's Initial Response
Samco responded the next day, acknowledging the issue and requesting additional technical details. I promptly replied with a detailed explanation of the vulnerability, including the URL structure and recommendations for securing the exposed data.
Date: Mon, 19 Aug 2024
From: CISO Samco <ciso@samco.in>
To: returntoshiganshina@protonmail.com
Subject: Re: URGENT: Critical Customer Data Exposure Discovered
Dear Shiganshina,
Thank you for bringing this serious issue to our attention. We acknowledge receipt of your email and appreciate your effort to report on the security vulnerability. Ensuring the security of our customers' data is a top priority for us.
Next Steps:
1. Immediate Action:
We are currently reviewing the details provided and taking immediate steps to secure the exposed data.
2. Bug Reporting Process:
Please share more details about the bug to ciso@samco.in. We would love to collaborate more with you to understand about the bug reported.
3. Secure Communication:
To facilitate further communication, please use ciso@samco.in to share any additional technical details.
We will keep you updated on our progress and aim to resolve this issue promptly.
Thank you for your cooperation and assistance in protecting our customers' privacy.
Regards,
ISMS Team,
Samco Securities"Dear Shiganshina,"
Very funny, Guess they aren't AOT fans.
Date: Mon, 19 Aug 2024
From: returntoshiganshina <returntoshiganshina@protonmail.com>
To: CISO Samco <ciso@samco.in>
Subject: Re: URGENT: Critical Customer Data Exposure Discovered
Dear Samco Information Security team,
Thank you for your prompt response. To illustrate the issue without compromising any specific customer's data, I can provide the general URL structure:
https://medial.samco.in/samco/client_pdf_esign/docs_XXXXXXX.pdf
Where 'XXXXXXX' represents a 7-digit number. Changing this number randomly has approximately a 10% chance of yielding another customer's data file. Considering there are 90 lakh 7-digit numbers, we estimate approximately 9 lakh customers may have their data publicly accessible.
Key points about this vulnerability:
1. These PDF files contain sensitive customer information, including KYC documents.
2. The files are publicly accessible without any authentication required.
3. The documents are currently indexed by search engines, making them discoverable.
I recommend you immediately restrict access to the files by requiring authentication, and de-index the files off search engines.
I want to emphasize the critical nature of this issue and the potential risks to your customers' privacy and security. I remain available to provide any further information or assistance you may need to address this vulnerability promptly and effectively.
Please keep me informed of the steps you're taking to resolve this issue. I look forward to hearing about your action plan and timeline for addressing this vulnerability.
Additionally, I was wondering if your company has a bug bounty program or a policy for recognizing security researchers who responsibly disclose vulnerabilities. If so, I would appreciate any information you can provide about this.
Thank you for your attention to this critical matter. I'm hopeful we can work together to ensure the security of your customers' data.
Sincerely,
A concerned student.Period of Silence and Further Attempts
After providing the requested details, Samco ceased communication. Despite sending multiple follow-up emails I received no response.
Date: Thu, 22 Aug 2024
From: returntoshiganshina <returntoshiganshina@protonmail.com>
To: CISO Samco <ciso@samco.in>
Subject: Re: URGENT: Critical Customer Data Exposure Discovered
Hi,
Kindly send an acknowledgment that you have received my previous email.Attempting to Report to CERT-In
After a week of being ignored by Samco, I decided to escalate the matter to CERT-In (Indian Computer Emergency Response Team). My initial attempt to email CERT-In failed due to their inbox being full, and the email bounced (What else can you expect from an Indian government agency?). This led to a temporary pause in my efforts.
Here's the email I'd sent:
Date: Wed, 28 Aug 2024
From: returntoshiganshina <returntoshiganshina@protonmail.com>
To: vdisclose@cert-in.org.in
Subject: [3] Urgent: Critical Data Exposure in Samco's Customer Portal
Dear CERT-In Team,
I am writing to report a critical data exposure vulnerability in Samco's customer portal. Despite notifying the company a week ago and providing detailed information, I have not received any update on remediation efforts. Given the severity of the exposure, I feel obligated to bring this to your attention.
The vulnerability affects Samco's web-based customer portal. Their website is samco.in, and they are a major trading platform. The company's customer portal is exposing sensitive KYC documents through publicly accessible and indexed PDF files. The vulnerability can be reproduced by accessing URLs with the following structure:
https://media1.samco.in/samco/client_pdf_esign/docs_XXXXXXX.pdf
Where XXXXXXX is a 7-digit number. Changing this number randomly has approximately a 10% chance of yielding another customer's data file. No authentication is required to access these files, and the documents are indexed by search engines, making them easily discoverable.
The impact of this vulnerability is severe. I estimate that approximately 9 lakh customers may have their sensitive data exposed. This includes KYC documents potentially containing Aadhar cards, PAN cards, bank statements, and other personally identifiable information. This exposure puts customers at risk of identity theft, financial fraud, and privacy violations.
In finding this breach, no specialized tools were used; the issue is replicable using any web browser. While I'm not aware of any current exploits, the simplicity of access makes exploitation trivial.
I initially notified the company on the 18th of August, and provided detailed information to their information security team on the 19th of August. However, I have not received any substantive response as of 28th August.
I am available to provide any additional information or assistance you may need. Please let me know if you require any clarification or further details.
Thank you for your prompt attention to this critical matter.
Sincerely,During this time, I also tried reaching out to a few news outlets, thinking they might cover the story and prompt action, but none of them replied either.
Date: Tue, Sep 10, 2024
From: returntoshiganshina <returntoshiganshina@protonmail.com>
To: tips@techcrunch.co
Subject: Urgent: Major Data Breach AFfecting 900,000 Indian Citizens
Dear Editor,
I am writing to bring to your attention a significant data security breach that potentially affects approximately 900,000 Indian citizens. This breach involves a prominent Indian stock trading website and exposes highly sensitive personal and financial information.
Key points:
...Renewed Efforts and Contacting CERT-In
Later, I received advice from a senior member of Cryptonite, Akash. He suggested two actions:
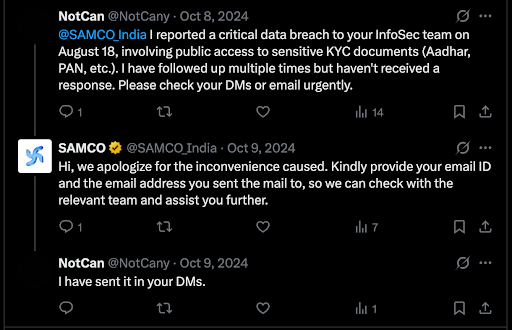
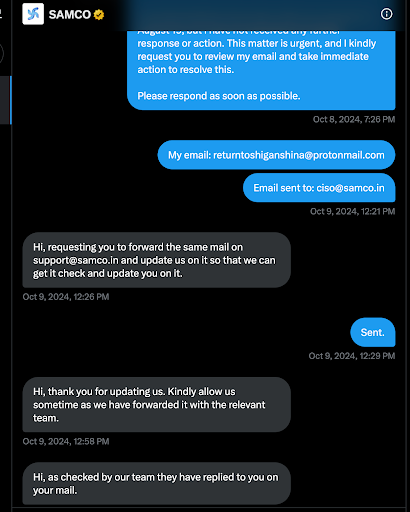
- Sent a direct message to Samco on Twitter.
- Used a secondary email address to contact CERT-In.
On October 9th, I followed up with Samco via Twitter and email. While Samco responded, they requested the same technical details I had already provided in earlier communications. I re-explained the issue, but once again, they stopped responding.
The fact that they sent a generic template without even filling it out correctly was a slap in the face. Seeing a placeholder like "[brief description of the issue]" where the details of a massive data breach should have been showed exactly how little they care about the whole ordeal.
Date: Wed, Oct 9, 2024
From: support@samco.in
To: returntoshiganshina@protonmail.com
Dear Client,
Bonjour from SAMCO Securities Ltd!
We appreciate your interest in our company and are happy to help answer any questions you may have.
We wanted to inform you that we have escalated the issue regarding [brief description of the issue to the concern department for further review.
Your commitment as a customer is much appreciated. We look forward to serving you again in the future!
You can visit the FAQ section on our website https://www.SAMCO.in/faq for any further reference.
Thanks & Regards,
Samco Securities Ltd
Email Assistance TeamSuccessful Intervention by CERT-In
CERT-In responded to my email sent to their secondary address and contacted Samco directly. With CERT-In's involvement, the vulnerability was finally fixed on October 21st, 2024, 64 days after my initial report.
Date: Thu, 17 Oct 2024
From: Incident <incident@cert-in.org.in>
To: returntoshiganshina, csirt finance, vdisclose
Subject: Critical Data Breach at Samco Securities Limited with Lakhs affected
Dear Sir/Madam,
Thank you for reporting to CERT-In.
You are requested to provide the relevant POC / Evidence (Sample 7-digit number) for further analysis.
Thanks and Regards,
CERT-In/CSIRT-Fin
Incident Response Help Desk
e-mail: incident@cert-in.org.in
Phone: 1800-11-4949
FAX: 1800-11-6969
Web: http://www.cert-in.org.in
PGP Fingerprint: A768 083E 4475 5725 B81A A379 2156 COCO B620 D0B4
PGP Key information: https://www.cert-in.org.in/s2cMainServlet?pageid=CONTACTUSAnd after providing them with a few samples,
Date: Mon, 21 Oct 2024
From: Incident <incident@cert-in.org.in>
To: returntoshiganshina, csirt finance
Subject: Critical Data Breach at Samco Securities Limited with Lakhs affected
Dear Sir/Madam,
With reference to trailing mail, the concerned organization has confirmed that reported vulnerability is fixed now.
You are requested to verify at your end and confirm.
Thanks and Regards,
CERT-In / CSIRT-FinRequest for Acknowledgement and Final Response from Samco
After the issue was resolved, I emailed Samco requesting a simple letter of acknowledgment for reporting the vulnerability. I was not seeking a bug bounty or any form of compensation, just formal recognition of my efforts. (Partly due to how calmly and dismissively they handled the situation, they would never pay a single cent.)
Date: Fri, 25 Oct 2024
From: returntoshiganshina <returntoshiganshina@protonmail.com>
To: support@samco.in
Subject: URGENT: Critical Customer Data Exposure Discovered
Dear Samco team,
I recently reported a critical security vulnerability that exposed KYC documents (Aadhar, PAN, bank statements) of approximately lakhs of customers following which the issue was fixed.
I followed responsible disclosure practices throughout notifying you first, maintaining confidentiality, and not accessing the exposed data.
Given the severity of this vulnerability, I request formal acknowledgment of this contribution. This could be in the form of:
A formal appreciation letter
A testimonial about the responsible disclosure
I look forward to your response. Thank you for your time.
Regards,
Harsh And AbhaySamco ignored my request for several weeks, despite multiple follow-up emails. Finally, on November 7th, 2024 (17 days after the fix), they responded, declining to provide any acknowledgment.
Date: Thu, 7 Nov 2024
From: support@samco.in
To: returntoshiganshina@protonmail.com
Dear Client,
Bonjour from SAMCO Securities Ltd!
We appreciate your interest in our company and are happy to help answer any questions you may have.
In reference to your email, we regret to inform you that we are unable to provide any form of acknowledgement at this time. We apologize for any inconvenience this may have caused.
Your commitment as a customer is much appreciated. We look forward to serving you again in the future!
You can visit the FAQ section on our website https://www.SAMCO.in/faq for any further reference.
Thanks & Regards,
Samco Securities Ltd
Email Assistance TeamConclusion
This experience was extremely frustrating and discouraging. Despite my efforts to report a serious vulnerability responsibly, I was met with prolonged silence and ghosted several times. In the end, it wasn't my report that prompted action, it was CERT-In's intervention that forced the issue to be addressed.
The most glaring issue, however, is that this was likely a problem they already knew about. Back in May 2024, several months prior to my discovery, multiple news outlets reported that approximately 3,000 Samco customer records containing similar types of data had surfaced on the dark web. At the time, Samco denied the incident and claimed they would conduct a "comprehensive review of their system".
Finding the exact same vulnerability just a few months later makes it painfully clear that their "comprehensive review" was nothing more than a PR move to save face. They didn't fix the leak when it first surfaced, and they didn't care to fix it when I pointed it out, until the government forced their hand.
Quick Timeline of Events
- August 18, 2024: Reported the data exposure to Samco.
- August 19, 2024: Samco replied, asking for more information. Sent technical details to Samco explaining the issue.
- (Numerous follow-up emails sent to Samco during this period received no response)
- October 9, 2024: Followed up with Samco via Twitter and email again.
- (Numerous follow-up emails sent to Samco during this period received no response)
- October 21, 2024: The vulnerability was fixed after CERT-In became involved.
- (Follow-up emails sent to Samco regarding acknowledgement)
- November 7, 2024: Samco replied, declining to provide any acknowledgement.
Special Thanks
- Abhay R.: Finding and documenting the breach with me
- Yvsr Akash: Advice on dealing with the breach leading to its resolution
- Aadit Agrawal: Help with documenting & Legal
References
Email Screenshots: https://docs.google.com/document/d/1RD5l7MiDarWB7yLQzaG37Am1Omezmz7VwU4LamGM000/